LNK Tabanlı Saldırılar Neden Hâlâ Engellenemiyor?
2025 yılının sonlarında, Arctic Wolf Labs, Belçika, Macaristan ve diğer Avrupa ülkelerindeki diplomatik kurumları hedef alan bir casusluk kampanyasına ilişkin bir araştırma yayınladı. UNC6384 olarak izlenen ve Çin bağlantılı bir grup olan bu tehdit aktörü, meşru Avrupa Komisyonu toplantıları ve NATO ile ilgili çalıştayları konu alan, zararlı Windows kısayol dosyaları (LNK dosyaları) dağıtmak için hedefli oltalama e-postaları kullandı.
Alıcı kısayola tıkladığında, gizli bir PowerShell komutu, sonunda PlugX uzaktan erişim truva atını yükleyen çok aşamalı bir bulaşma zincirini başlattı. Kampanya, Mart 2025’te açıklanan ve bir LNK dosyasının komut satırı argümanlarındaki boşluklarla gizlenerek komutların gizlice yürütülmesini sağlayan ZDI-CAN-25373 adlı Windows kısayol güvenlik açığını istismar etti.
UNC6384’ün bu dosyayı kullanması, daha geniş kapsamlı bir sorunu gözler önüne serdi: Kısayol dosyaları, kullanıcılar tarafından hâlâ sıradan bir unsur olarak görülüyor ve genellikle yürütülebilir dosyalara veya makro içeren belgelere kıyasla daha az dikkatle inceleniyor. Kötü amaçlı bir LNK dosyası çalıştırıldığında, en tehlikeli faaliyetler genellikle çalışma zamanında şifrelenmiş komut dosyaları, aşamalı arşivler ve imzalı ikili dosyaların kötüye kullanılması yoluyla ortaya çıkıyor; bu durumlarda statik tarama ve itibar kontrolleri, bu tehditlere ayak uydurmakta zorlanabiliyor.
Kampanya o zamandan beri gelişmeye devam ediyor. Nisan 2026’da The Hacker News, sektörde TA416 olarak bilinen aynı tehdit grubunun, 2025 ortasından itibaren Avrupa’daki hükümet ve diplomatik kuruluşları yeniden hedef almaya başladığını bildirdi. Grup, PlugX yükünü güncellemeye devam ederken, OAuth yönlendirme suistimali, Cloudflare Turnstile doğrulama sayfaları ve MSBuild tabanlı yürütme gibi yeni dağıtım yöntemlerini de kullanmaya başladı.
Bu makalede incelenen Arctic Wolf araştırması, günümüzde belgelenmiş ve halen devam eden bir operasyonun bir aşamasını ele almakta ve MetaDefender ile Deep CDR™ Teknolojisinin birlikte nasıl algılama ile önleme arasındaki boşluğu kapattığını göstermektedir.
UNC6384 Saldırı Zinciri
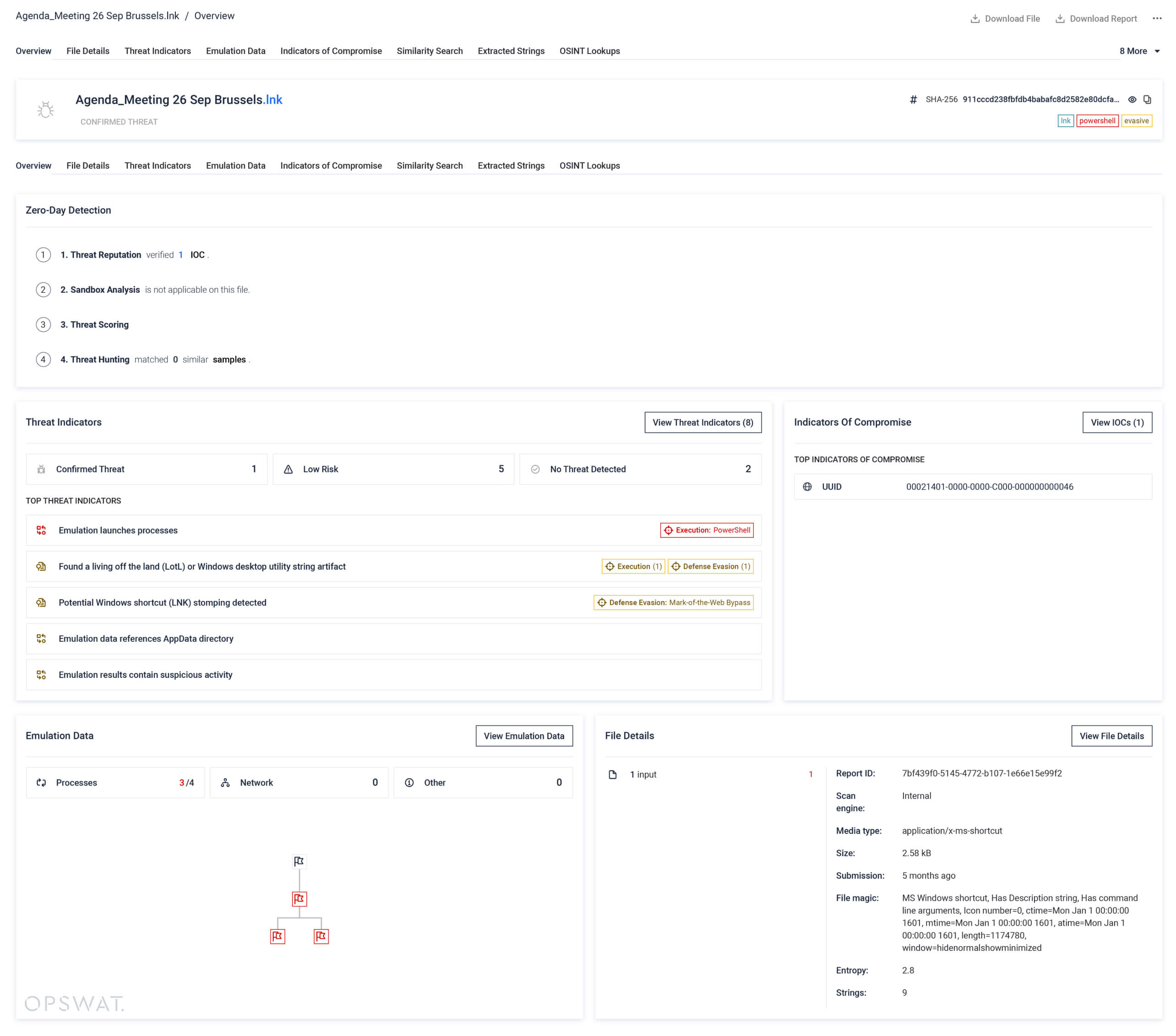
Her şey, çoğu kullanıcının asla şüphe duymayacağı bir dosyayla başladı. Bu kampanyada dağıtılan ve "Agenda_Meeting 26 Sep Brussels.lnk" adlı LNK dosyası, yalnızca 2,58 KB büyüklüğündeydi ve AB ile Batı Balkanlar arasındaki sınır geçiş noktalarında malların serbest dolaşımının kolaylaştırılmasına yönelik gerçek bir Avrupa Komisyonu toplantısına atıfta bulunuyordu. Bu, gerçek bir etkinliğin gerçek gündemiydi ve kısayol da sıradan bir dosya gibi görünüyordu.
1. Aşama: Kötü amaçlı LNK dosyası aracılığıyla ilk erişim
Alıcı kısayola çift tıkladığında, sistem sessizce PowerShell'i çalıştırdı ve şifrelenmiş bir komutla bir tar arşivini (rjnlzlkfe.ta) çözüp kullanıcının yerel Temp dizinine çıkardı. Ardından PowerShell komutu, tar.exe dosyasını kullanarak arşivi açtı ve içeriği çalıştırırken, aynı anda gerçek toplantı gündemini gösteren sahte bir PDF dosyasını da açtı. Kurban bir belge gördü. Saldırgan ise kod yürütme yetkisi elde etti.
2. Aşama: İmzalanmış ve geçerli bir ikili dosya aracılığıyla DLL yan yükleme
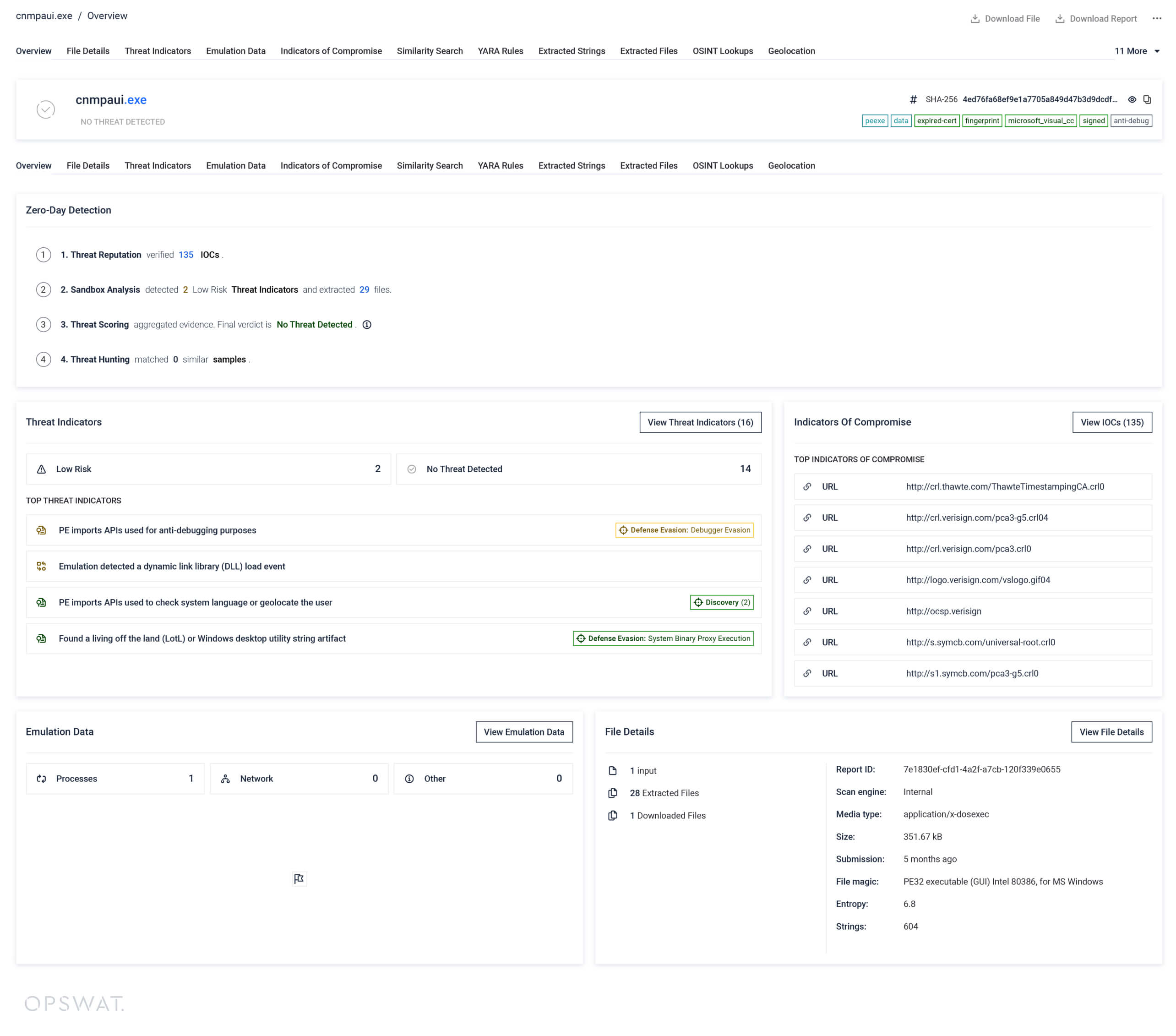
Açılan arşivde üç dosya bulunuyordu: cnmpaui.exe, cnmpaui.dll ve cnmplog.dat. Bunlardan ilki, Canon Inc. tarafından Symantec tarafından verilen bir sertifika ile dijital olarak imzalanmış, meşru bir Canon yazıcı yardımcısı programıdır. İmza geçerlidir çünkü sertifikanın hala aktif olduğu bir tarihte zaman damgası eklenmiştir; bu da, sertifikanın süresi 2018’de dolmuş olsa da (Arctic Wolf) Windows’un bu dosyaya güvenmeye devam ettiği anlamına gelir.
İşte burada hassasiyet önem kazanıyor. EXE dosyası zararlı değildir. Bu, belirli bir amaç için kötüye kullanılan gerçek bir Canon yardımcı programıdır: cnmpaui.exe çalıştırıldığında, sistem yollarını kontrol etmeden önce kendi dizininde cnmpaui.dll dosyasını arar. UNC6384, meşru ikili dosyanın yanına aynı isimde zararlı bir DLL dosyası yerleştirerek bu arama sırasını ele geçirdi ve güvenilir bir işlem içinde kendi kodunu yükledi.
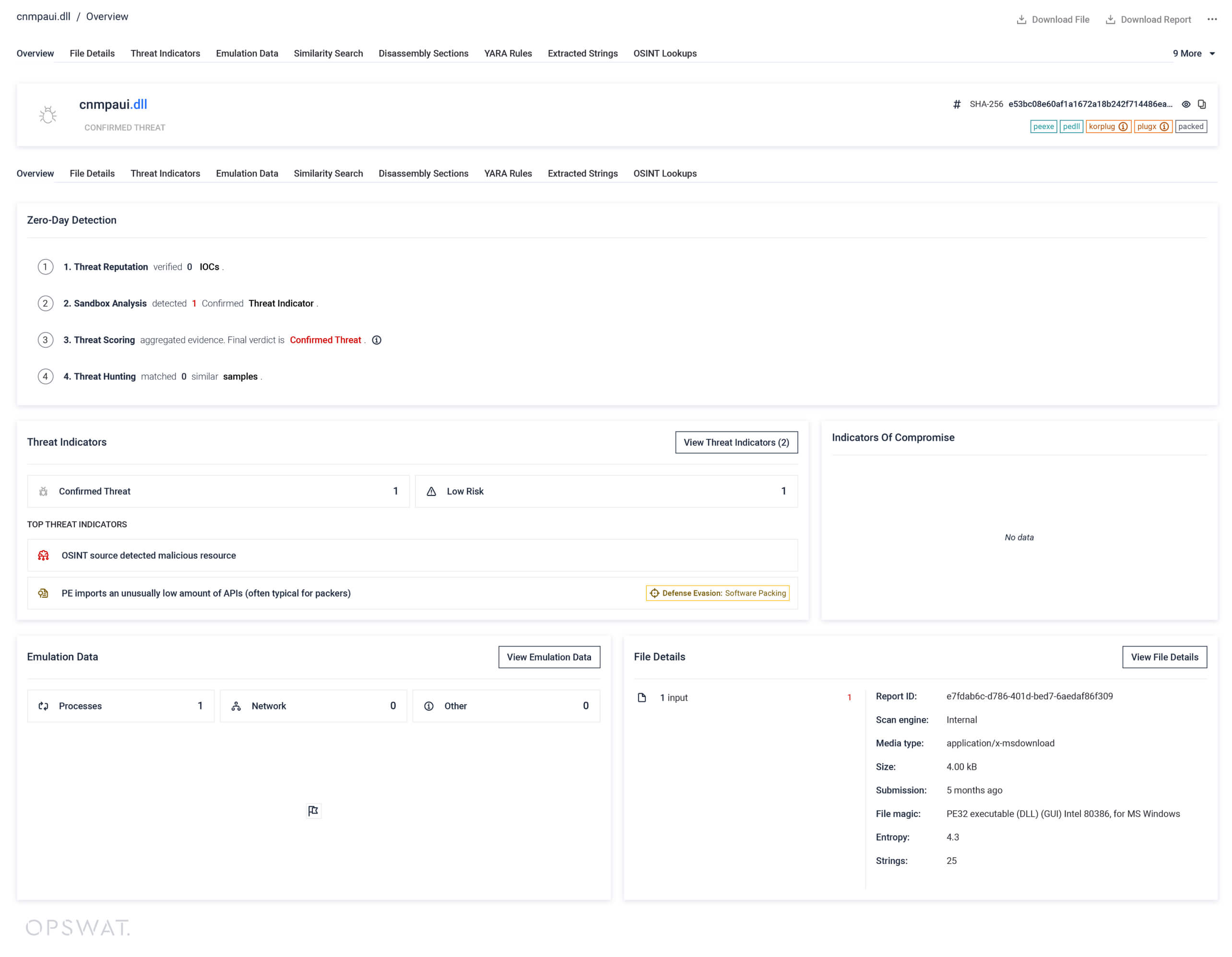
3. Aşama: Yükün şifresinin çözülmesi ve PlugX'in çalıştırılması
Kötü amaçlı cnmpaui.dll dosyası, Ekim 2025 varyantında sadece 4 KB boyutunda olan ve tek bir amaca hizmet etmek üzere tasarlanmış hafif bir yükleyicidir: üçüncü dosya olan cnmplog.dat’ın şifresini çözmek ve çalıştırmak. Bu dosya, PlugX uzaktan erişim truva atını içeren RC4 şifrelemeli bir blobdur. Yükleyici, sabit kodlanmış 16 baytlık bir anahtar kullanarak bu dosyanın şifresini çözer ve ortaya çıkan yükü doğrudan meşru cnmpaui.exe işleminin bellek alanına eşler.
O andan itibaren PlugX, imzalanmış ve güvenilir bir ikili dosya içinde çalışır. "CanonPrinter" adlı bir kayıt defteri Run anahtarı aracılığıyla kalıcılık sağlar, ortama uyum sağlamak için "SamsungDriver" veya "DellSetupFiles" gibi adlara sahip gizli dizinler oluşturur ve normal web trafiğine karışmak için rastgele URL yolları ve sahte bir Internet Explorer kullanıcı ajanı dizesi kullanarak 443 numaralı bağlantı noktası üzerinden HTTPS üzerinden komuta ve kontrol altyapısıyla iletişim kurar.
İlk tıklamadan aktif bir arka kapıya kadar, bu zincirdeki hiçbir unsur ilk bakışta açıkça zararlı görünmüyordu ve gerçekten şüpheli davranışların çoğu yalnızca çalışma sırasında ortaya çıktı. Her aşama, statik incelemede normal görünmek ve geleneksel filtrelerin taramadığı yerlerde çalışmak üzere tasarlanmıştı.
Neden Statik Savunmalar Bu Zincirle Zorlanıyor?
Statik savunma sistemleri bu zincirle başa çıkmakta zorlanır, çünkü her aşama tek başına bakıldığında makul görünecek şekilde tasarlanmıştır. Kampanyayı etkili kılan şey, tek bir bariz kötü amaçlı dosya değil, gerçek niyetleri ancak çalışma sırasında ortaya çıkan, güvenilir görünümlü bileşenlerden oluşan bir dizidir. Bu model kısayol dosyalarıyla sınırlı değildir: Saldırganlar, geleneksel antivirüs algılamasından kaçınmak için, görünüşte zararsız resim dosyalarının içine de yükleri gizlemiş ve bunları LNK tabanlı dağıtım yöntemiyle birleştirmiştir.
Neden Statik Savunmalar Bu Zincirle Zorlanıyor?
| Sahne | Savunmacının Gördükleri | Neden Denetimden Geçiyor? |
|---|---|---|
| Zararlı LNK dosyası | Bir diplomatik toplantıya atıfta bulunan 2,58 KB'lık bir kısayol dosyası | LNK dosyaları varsayılan olarak düşük risklidir; ZDI-CAN-25373, PowerShell komutunu çoğu meta veri denetleyicisinin ayrıştırmadığı boşluklarla doldurarak gizler. |
| Canon EXE imzalı | Tanınmış bir yayıncıdan alınmış, geçerli ve zaman damgası içeren bir dijital imzaya sahip meşru bir PE32 ikili dosyası | Bunu engellemek, Canon yazıcı yazılımını çalıştıran her ortamı sorunlu olarak işaretler. İtibar motorlarının buna güvenmemesi için hiçbir neden yoktur. |
| 4 KB'lık yükleyici DLL dosyası | Açıkça şüpheli görünen hiçbir içe aktarma içermeyen, tek görevi okumak, şifresini çözmek ve yürütmeyi devretmek olan minimal bir DLL | YARA kuralları bilinen varyantları tespit edebilir, ancak farklı bir anahtar veya şifre çözme rutini içeren yeniden derlenmiş bir yükleyici, statik kapsamdan kaçabilir. |
| Şifrelenmiş PlugX yükü | Şifresi çözülmüş haliyle diske hiç yazılmayan, içeriği gizli bir .dat dosyası | Dosya tabanlı tarama, kötü amaçlı yazılımın kendisini asla incelemez. Yük, doğrudan güvenilir Canon işleminin bellek alanına yüklenir. |
Statik araçların inceleyebildikleri ile çalışma zamanında gerçekte neler olup bittiği arasındaki bu uçurum, aldatıcı kampanyaların başarılı olabildiği alandır. Bu uçurumu kapatmak için, ilk dosya çalıştırılmasından sonraki her aşamaya kadar tüm yürütme yolunu gözlemleyebilen ve görünüşten ziyade davranışa dayalı bir değerlendirme yapabilen bir tespit yaklaşımı gereklidir.
MetaDefender , Zincirin Tamamını Nasıl Ortaya Çıkarıyor?
MetaDefender , OPSWAT tek bir güvenilir karar vermeden önce her dosyayı farklı açılardan incelemek üzere dört analiz katmanını bir araya getiren, bütünleşik sıfırıncı gün algılama çözümüdür.
- Tehdit itibar analizi, dosyanın hash değerlerini, meta verilerini ve gömülü göstergelerini 50 milyardan fazla göstergeden derlenen küresel istihbarat verileriyle karşılaştırır. Bu süreç, halihazırda bilinen unsurları tespit etmeye ve bilinmeyenlere bağlam kazandırmaya yardımcı olur.
- Adaptive , daha sonra dosyayı sanal bir ortamda çalıştırır ve çalışma zamanı akışını izler: LNK dosyasının PowerShell’i başlatması, şifrelenmiş komutun bir tar arşivini açması, imzalı Canon ikili dosyasının imzalanmamış bir DLL’yi yüklemesi ve şifresi çözülmüş PlugX yükünün kalıcılık sağlaması ve C2 (komuta ve kontrol) altyapısına bağlanması.
- Tehdit puanlaması, bu sonuçları, itibar sinyallerini ve çıkarılan göstergeleri, davranışsal bağlamın tamamını dikkate alan ağırlıklı bir risk puanı halinde birleştirir.
- Makine öğrenimi tabanlı benzerlik araması, dosyayı ve davranışını bilinen kötü amaçlı yazılım aileleriyle ve ilgili faaliyetlerle karşılaştırarak, PlugX varyantlarına veya benzer DLL yan yükleme kampanyalarına ilişkin bağlantıları ortaya çıkarmaya yardımcı olur.
Bu çözüm, %99,9'a varan sıfırıncı gün saldırı tespit etkinliği sunarken, SOC analistlerini ayrı raporları manuel olarak karşılaştırmaya zorlamak yerine dosya başına tek bir güvenilir sonuç verir. Bu özellik, ekipler e-posta, MFT, ICAP, kiosklar, depolama ve etki alanları arası iş akışları üzerinden günde yüzlerce dosyayı öncelik sırasına koyarken büyük önem taşır.
Bu zincirdeki en önemli ayırt edici özellik, komut düzeyinde emülasyondur. Eski nesil sanal makine tabanlı sanal ortamlar, tam yürütmeyi engellemek için sanal makine kaçırma teknikleri, zamanlama gecikmeleri ve ortam kontrolleri kullanan kötü amaçlı yazılımları tespit edemeyebilir. MetaDefender uyarlanabilir sanal ortamı, CPU ve işletim sistemi davranışını komut düzeyinde taklit eder; bu da LNK’dan PowerShell’e ve oradan da DLL’ye uzanan tüm yan yükleme dizisini ortaya çıkarmaya yardımcı olur.
SOC ekipleri için bunun getirisi somuttur:
- Karar önceden ilişkilendirilmiş ve MITRE sınıflandırmasına göre düzenlenmiş olduğundan, triyaj süreci daha hızlı gerçekleşir
- Karar, yalnızca statik itibarı değil, çalışma zamanı davranışını da yansıttığı için daha sağlam engelleme kararları
- MetaDefender , kötüye kullanılan geçerli ve imzalanmış bir ikili dosya ile gerçekten kötü amaçlı bir yük arasında ayrım yapabildiğinden, yanlış pozitif sonuçlar azalmıştır
- Bu saldırıların ortama sızdığı dosya alım noktalarında sıfırıncı gün saldırılarına karşı daha iyi hazırlık
Deep CDR™ Teknolojisi Tetikleyiciyi Nasıl Etkisiz Hale Getirir?
Deep CDR™ Teknolojisi, tüm süreci başlatan dosyayı etkisiz hale getirerek bu zincirleme reaksiyonu daha başlamadan durdurur. MetaDefender , kötü amaçlı bir dosyanın çalışma sırasında ne yaptığını ortaya çıkarırken, Deep CDR™ Teknolojisi ise dosyanın hiçbir şekilde çalıştırılma şansı bulmamasını sağlar.
Bu mekanizma, LNK tabanlı saldırıların işleyişine özgüdür. Silah olarak kullanılan bir kısayol, kötü niyetli amacını gömülü komut satırı argümanlarında taşır; bu örnekte, tar arşivini açan ve yük zincirini başlatan şifrelenmiş PowerShell çağrısı söz konusudur. Deep CDR™ Teknolojisi, bu gömülü komutu tespit eder ve onu zararsız bir sahte komutla değiştirir; böylece kısayolu temizlenmiş haliyle korurken, saldırı tetikleyicisi olarak işlev görme yeteneğini ortadan kaldırır.
Sonuç olarak, yürütme öncesinde orijinal zararlı davranışların etkisiz hale getirildiği, güvenli hale getirilmiş bir LNK iş akışı ortaya çıkmaktadır. PowerShell komutları çalıştırılmaz, arşivler açılmaz, DLL dosyaları yan yükleme yoluyla yüklenmez ve PlugX etkinleştirilmez. MetaDefender ile Deep CDR™ Teknolojisi bir araya geldiğinde, iki katmanlı bir savunma modeli oluşturur.
İki Katmanlı Savunma Modeli
| Katman | Teknoloji | Rol |
|---|---|---|
| Tespit et ve anla | MetaDefender | Dosyayı çalıştırır, çok aşamalı yürütme yolunun tamamını ortaya çıkarır, davranışsal IOC’leri çıkarır ve tek bir güvenilir sonuç döndürür. |
| Etkisiz hale getirmek ve önlemek | Derin CDR™ Teknolojisi | Kötü amaçlı LNK komutunu etkisiz hale getirerek kısayolun çalıştırılmasını engeller. |
Bu ayrım pratikte büyük önem taşır. MetaDefender , özellikle çalışma zamanı davranışını anlamak ve kesin bir karar vermek istendiğinde, derinlemesine analiz gerektiren dosyalar için geliştirilmiş bir sıfırıncı gün algılama çözümüdür. Deep CDR™ Teknolojisi ise, içeriği meşru kullanımları engellemeden güvenli bir şekilde etkisiz hale getirilebilen dosyalar için tasarlanmış bir temizleme ve önleme kontrolüdür. Bu iki çözüm bir araya geldiğinde, sorunun her iki yönünü de ele alır: bir tehdidin ne yaptığını anlamak ve ona asla fırsat vermemek.
Hassasiyet Neden Önemlidir?
Hassasiyet önemlidir, çünkü bir saldırı zincirindeki her dosya zararlı değildir ve hepsine aynı şekilde yaklaşmak, araçlarınıza duyulan güveni sarsan aşırı geniş kapsamlı algılamalara yol açar. Bu kampanya bunu açıkça ortaya koyuyor.
İmzalanmış Canon yazıcı yardımcı programı (cnmpaui.exe), meşru bir ikili dosyadır. Geçerli bir dijital imzaya, temiz bir itibar geçmişine ve meşru yazılımlarla ilişkili bir hash değerine sahiptir. Bu dosyayı kötü amaçlı olarak işaretlemek, Canon yazıcı yazılımının kurulu olduğu ortamlarda yanlış pozitif sonuçlara yol açacak ve SOC analistlerinin aldıkları uyarıları güvenilmez bulmalarına neden olacaktır.
Başlıca IOC’ler (tehlike göstergeleri), kötü amaçlı DLL dosyası (cnmpaui.dll) ve bunun tetiklediği davranış zinciridir:
- Şifrelenmiş bir yükün sabit kodlanmış bir RC4 anahtarıyla yan yükleme ve şifresinin çözülmesi
- Şifresi çözülmüş PlugX ikili dosyasını güvenilir bir işlemin bellek alanına eşleme
- "CanonPrinter" Çalıştır anahtarı aracılığıyla kalıcılık sağlanması
- Rastgele URL yolları ve sahte kullanıcı ajanı dizesi kullanılarak HTTPS C2 trafiğinin başlatılması
En önemli sinyaller bunlardır ve bunlar ancak bir algılama aracı davranışları gözlemleyip, kötüye kullanılan güvenilir bir ikili dosya ile gerçekten kötü amaçlı bir öğeyi birbirinden ayırt edebildiğinde ortaya çıkar.
İşte bu noktada MetaDefender tek bir güvenilir karar vermesi özellikle değer kazanıyor. Algılama süreci, zincirdeki her dosyaya genel bir “zararlı” etiketi atamak yerine, her bir bileşeni tam yürütme bağlamı içindeki gözlemlenen davranışına göre puanlıyor.
İmzalı EXE dosyası, yan yükleme amacıyla kullanılan meşru bir ikili dosya olarak tanımlanmaktadır. DLL dosyası ve bunun yol açtığı çalışma zamanı davranışları ise gerçek tehdit olarak işaretlenmektedir. Bu ayrım, güvenlik ekiplerine daha net bir görünüm sunar ve sinyali gürültüden ayırmak için gereken manuel çabayı azaltır.
Kötü amaçlı DLL'lerin statik tespiti, YARA gibi hedef odaklı kurallarla da güçlendirilebilir; Arctic Wolf'un CanonStager yükleyicisi için yayınladığı YARA imzaları bu konuda yararlı bir başlangıç noktasıdır. Ancak imza tabanlı tespit, doğası gereği reaktif bir yaklaşımdır. Bu tür bir zincirde asıl farkı yaratan unsur, davranışsal görünürlük ve dosya etkisizleştirmedir.
LNK Tabanlı Saldırı Zincirlerini Ortaya Çıkarmak İçin Katmanlı Dosya Güvenliği Uygulaması
LNK tabanlı saldırılar, insanların her gün gördüğü ve nadiren tehlikeli olarak değerlendirdiği bir dosya türüne dayandıkları için hâlâ etkili olmaya devam ediyor. Önceki bir makalede, LNK dosyalarının sıradan Windows kısayolları olduğunu ve saldırganların bunların içine PowerShell veya cmd.exe komutlarını gizleyerek, bazen dosya açılana kadar zararsız görünen şekillerde silah olarak kullanabileceğini belirtmiştik. İşte bu yüzden UNC6384 gibi kampanyalar başarılı olmaya devam ediyor: kısayol tanıdık görünüyor, ancak tetiklediği davranış hiç de öyle değil.
Bu eğilim birçok saldırı kampanyasında da kendini göstermiştir. Emotet ile ilgili haberimizde, kısayol dosyalarının normal belgelerden ayırt edilmesinin neden zor olduğunu ve Windows’ta bu dosyaların uzantılarının varsayılan olarak görüntülenmediğini açıklamıştık. Bu durum, söz konusu dosyaları bulaşma aracı olarak özellikle etkili hale getiriyordu. Buradan çıkarılacak ders de aynıdır: Saldırganların, tanıdık bir dosya türünün hâlâ günlük iş akışlarına sızıp çok aşamalı bir bulaşma zincirini başlatabildiği durumlarda yepyeni bir hileye ihtiyacı yoktur.
Çözüm, zincirdeki her dosyayı kötü amaçlı olarak etiketlemek değildir. Çözüm, çalışma zamanı davranışını ortaya çıkarabilen, kötüye kullanılan meşru bir ikili dosya ile kötü amaçlı bir yük arasında ayrım yapabilen ve tetikleyici devreye girmeden önce onu durdurabilen katmanlı dosya güvenliği uygulamaktır. MetaDefender ve Deep CDR™ Teknolojisinin ekibinizin LNK tabanlı saldırıları tespit etmesine, analiz etmesine ve önlemesine nasıl yardımcı olabileceği konusunda bir OPSWAT görüşün.